SSO with DUO Option 1 – Duo Generic OIDC Relying Party
This page provides step-by-step instructions for configuring Duo Security as the single sign-on provider for xAssets using the "Generic OIDC Relying Party" application. This is the preferred Duo option because Duo handles the entire authentication flow, collecting both the username/password and processing the two-factor authentication (2FA) workflow.
For the alternative Duo option where xAssets collects the username before handing off to Duo, see SSO with Duo Option 2.
Prerequisites
- A Duo Security account with administrator access
- The "Generic OIDC Relying Party -- Single Sign-On" application available in your Duo plan
- Configuration-level access to xAssets
- The SSOADMIN account created and in the Admins group (see SSO Introduction and Setup)
Step 1: Enable the OIDC Application in Duo
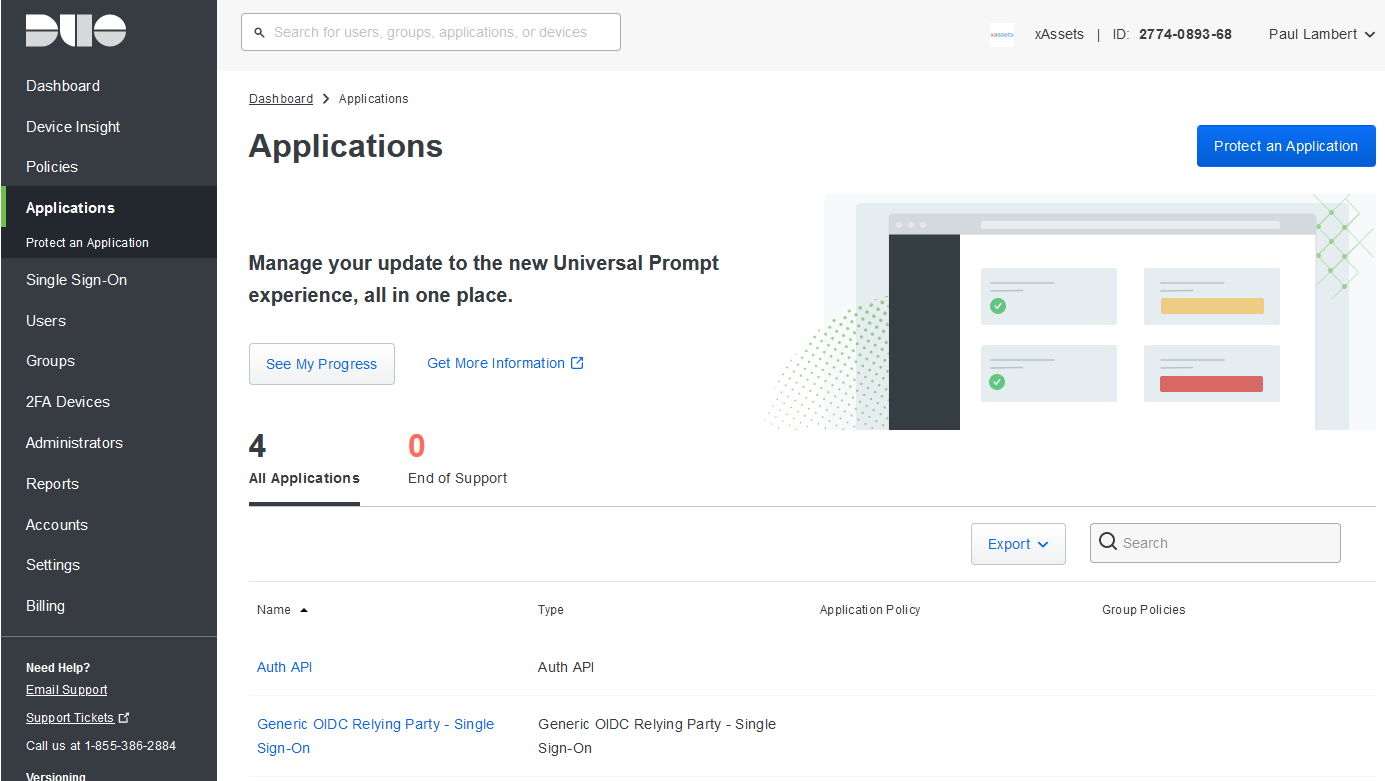
- Log in to the Duo Admin Panel
- Navigate to Applications > Protect an Application
- Find and enable the Generic OIDC Relying Party -- Single Sign-On application
Step 2: Configure OIDC Scopes
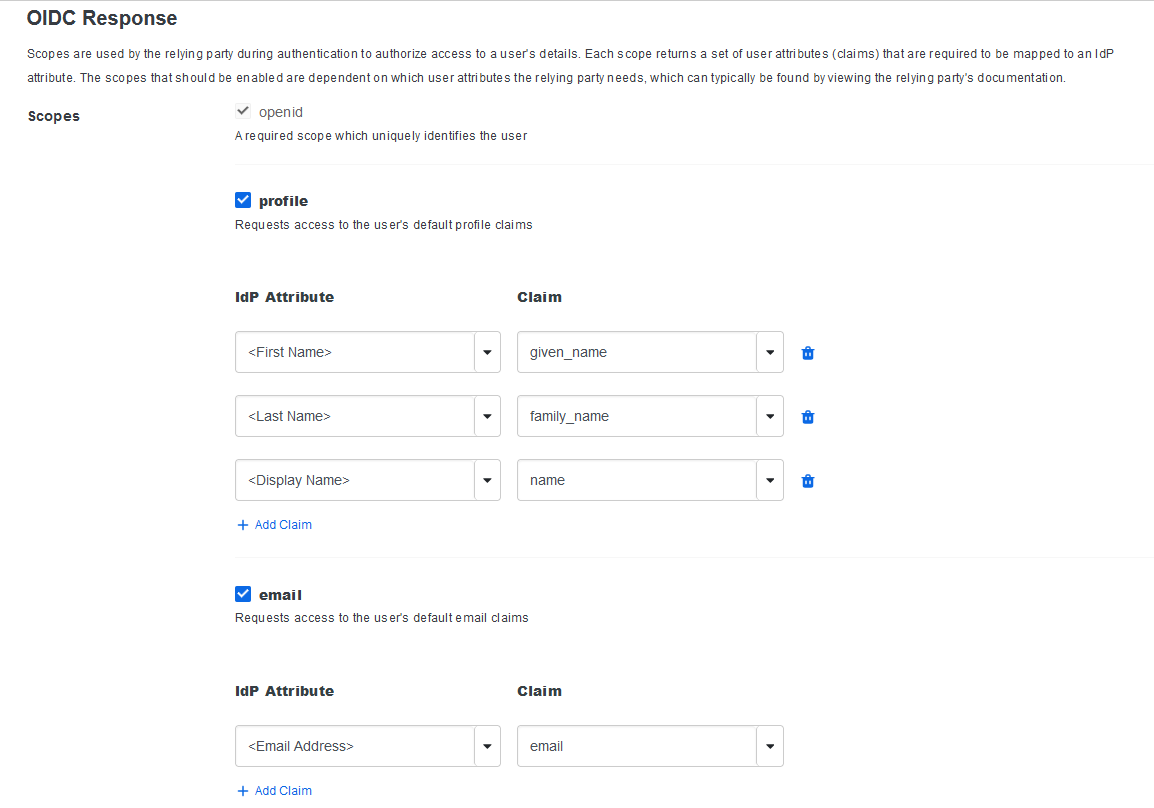
- In the Duo Admin Panel, click into the application
- Navigate to OIDC Response > Scopes
- Ensure the following scopes are enabled: openid, profile, and email
Step 3: Set the Redirect URL
- In the application configuration, set the Sign in Redirect URLs to:
https://yourinstancename.hostedprefixname.xassets.net/a.aspx
Replace yourinstancename with your actual xAssets instance name.
- Click Save at the bottom of the page
Step 4: Note the Connection Details
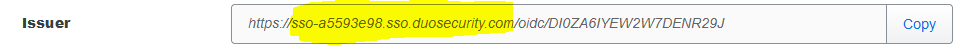
From the Duo Admin Panel application page, note the following values:
- SSO Domain -- the domain part of your Duo SSO addresses, in the format
sso-xxxxxxxx.sso.duosecurity.com. You can find this in any of the URLs shown on the Generic OIDC Relying Party screen.
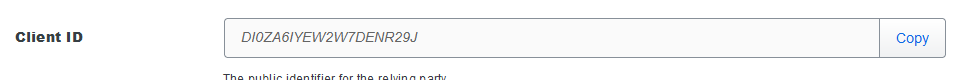
- Client ID:
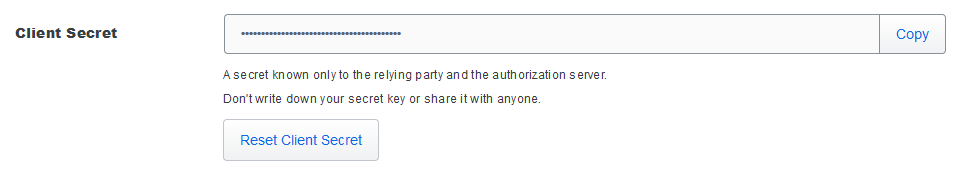
- Client Secret:
Step 5: Configure xAssets
- Log in to xAssets as a configuration-level user
- Navigate to Admin > Settings
- Set the AUTHENTICATIONTYPE SpecialOption to DUO GENERIC
Step 6: Create a Credential Pack in xAssets
- Navigate to Discover > Prepare > Credentials
- Click Create Credentials
- Configure the credential pack as follows:
| Field | Value |
|---|---|
| Credential Type | Named Credentials |
| Collection Server | Application Server |
| Pack Name | DUOGENERIC-SSO |
| Domain Name | The Duo SSO Domain (e.g., sso-xxxxxxxx.sso.duosecurity.com) |
| Username | The Client ID from Step 4 |
| Password | The Client Secret from Step 4 |
- Save the credential pack and verify it appears when you refresh the credentials list
Step 7: Test the Login
- Open a new private/incognito browser window
- Navigate to your xAssets URL
- Duo should present its login page, collecting username, password, and 2FA
- After successful authentication, you should be returned to xAssets and logged in
If the login fails, see Troubleshooting. To log in without Duo for troubleshooting:
https://myinstance.clustername.xassets.net/a.aspx?logondirect=direct
Note: Other options on the Duo configuration page may be changed, but the settings described above represent the tested configuration for the xAssets integration with Duo.
Related Articles
- SSO with Duo Option 2 — the alternative Duo integration method
- SSO Introduction and Setup — general SSO enablement steps
- Troubleshooting — diagnosing login failures