Installations, Moves, Additions and Changes (IMACS)
The IMAC report tracks all infrastructure changes over a rolling 30-day window, categorised into Installs, Moves, Adds, Changes, and Disposes (the ITIL "IMAC-D" model). This structured view is essential for IT governance, audit compliance, and understanding how your environment evolves over time.
Accessing the IMAC Report
The report is exposed in three places, each scoped to a different asset population:
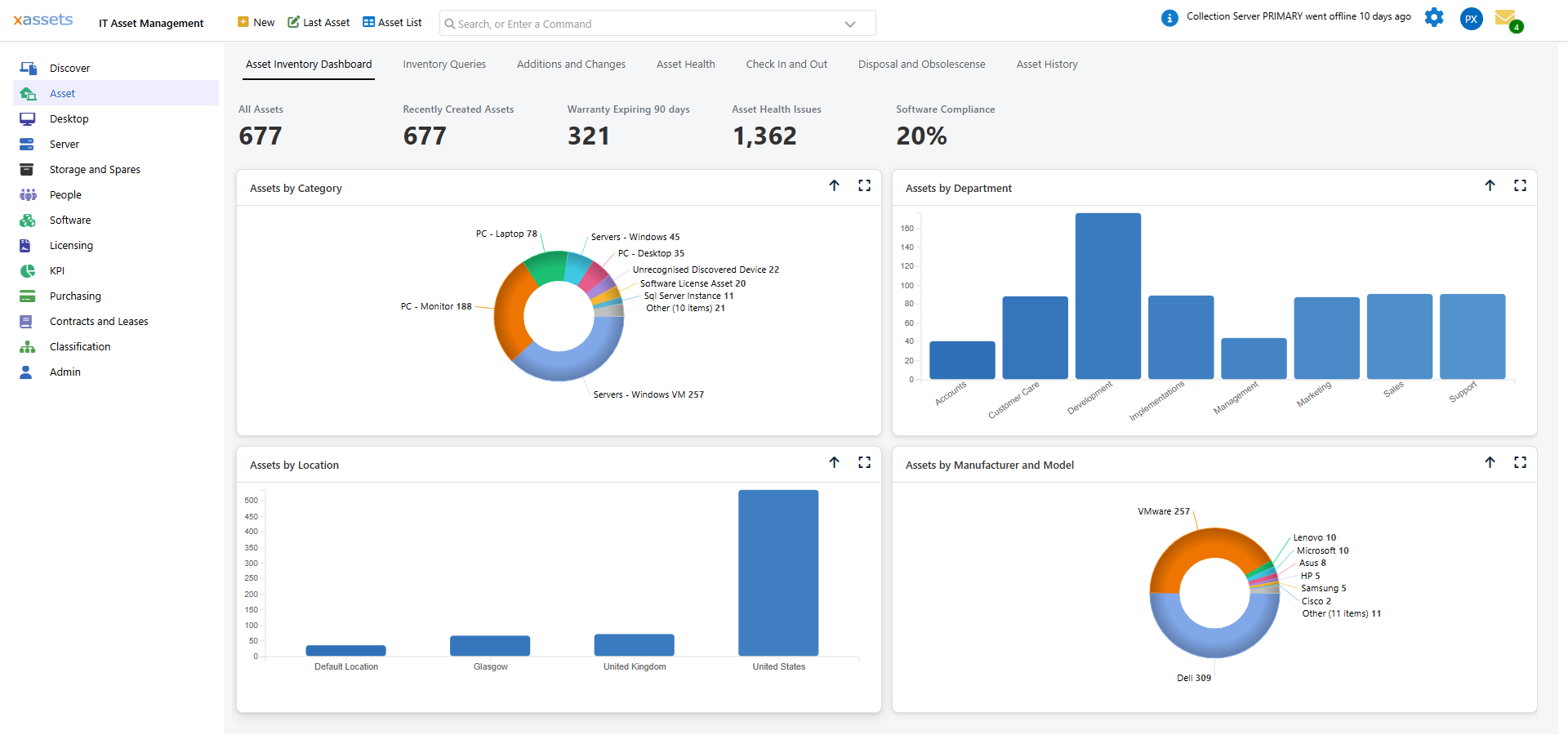
- Asset > Asset Inventory Dashboard > Additions and Changes — all configuration items
- Desktop > Desktop Dashboard > Additions and Changes — desktops and laptops only
- Server > Server Dashboard > Additions and Changes — servers only
Each dashboard contains three panels: a 7-day Additions list, a 7-day Software Installations list, and the full IMAC report (last 30 days).
Scope
The IMAC report covers Configuration Items (CIs) only -- assets with a Network Discovery code other than "SW" in their category. This means it focuses on physical and virtual infrastructure (computers, servers, network devices) rather than software licence records.
IMAC Categories
Each row in the report is tagged with one of these change types:
| Type | Changes Tracked |
|---|---|
| PC Install | A new asset record was created within the reporting window. To avoid noise, no individual hardware or software rows are emitted for brand-new assets — one "PC Install" row covers the whole device. |
| Move | Location changed |
| Memory Change | Memory slots added or removed |
| CPU Change | CPUs added or removed |
| Disk Change | Disks added or removed |
| Software Install | A Primary or Banned-software product was newly detected on an existing asset |
| Software Removal | A Primary or Banned-software product disappeared from an existing asset |
| Other | Operating System, Domain, Custodian, Cost Centre, Department, or Status changed |
| Dispose | DateDisposedOf was newly set |
Each row also records the field that changed, the old and new values, who changed it, and whether the change came from manual editing, discovery, or a system process.
Customisation
The IMAC report is implemented as a single SavedSelect (IMACS Report, IMACS Report - Desktop, IMACS Report - Server). To track additional change types — for example IP address changes or warranty updates — extend the underlying SQL with another union all block following the existing pattern.
Using IMAC Reports
| Use Case | How |
|---|---|
| Audit preparation | Generate an IMAC report for the audit period to demonstrate what changed and when |
| Change verification | After a planned project (e.g., memory upgrades across a department), run the IMAC report to confirm the changes were applied |
| Trend analysis | Compare IMAC reports across periods to identify patterns (e.g., increasing rate of hardware additions may indicate growth) |
| Security review | Look for unexpected changes that may indicate unauthorised modifications |
Tips
- Use the Desktop or Server dashboard variant when you only need to see one population — they apply the same change logic but restrict to desktops/laptops or servers
- Run IMAC reports monthly and archive them for audit purposes
- If the report is very long, filter by Type (Installs only, Moves only, etc.) to focus on specific change types
- Compare IMAC data with change requests to verify that all recorded changes were authorised
Related Articles
- Additions and Changes — the broader change reporting dashboard
- Asset History — viewing change history for a specific asset
- Email Notifications — automated alerts for specific change types